Babel Obfuscator
Protect your software against reverse engineering to safeguard the intellectual property of your code
The Obfuscator for .NET
Babel Obfuscator is a powerful protection tool for the Microsoft .NET Framework. Programs written in .NET languages, like C# and Visual Basic .NET, are normally easy to reverse engineer because they compile to MSIL (Microsoft Intermediate Language), a CPU-independent instruction set that is embedded into .NET assemblies, along with metadata allowing the reconstruction of original source code. Babel Obfuscator is able to transform assemblies in order to conceal the code, so that reversing is extremely difficult. This transformation process is called obfuscation.
General Features
Protects your code and intellectual property against Reverse Engineering
Compatible with all .NET Framework technologies
- From .NET 10.0 to .NET 5.0
- .NET Core 2.x, 3.x
- .NET Standard 1.x, 2.x
- .NET Framework from v2.0 to v4.x
- .NET MAUI
- ASP.NET
- Blazor
- Xamarin for Android and iOS
- Universal Windows Platform
- Mono
- nanoFramework
- Silverlight
- Unity
Runs on Windows, MAC OSX and Linux operating systems
Fully managed code encryption and virtualization
Simplify the deploy of your application merging or embedding all dependencies into a single file
Performs code optimization by reducing the overall metadata size and removing unused code
Integrated with Visual Studio tools family, Azure DevOps, AppCenter, MSBuild and command line
Available also as dotnet CLI global tool

Obfuscation and Protection
Babel Obfuscator provides an incredible number of features which can be easily accessed from the command line and also from a stunning graphical interface. Please take a look at the following list of available features
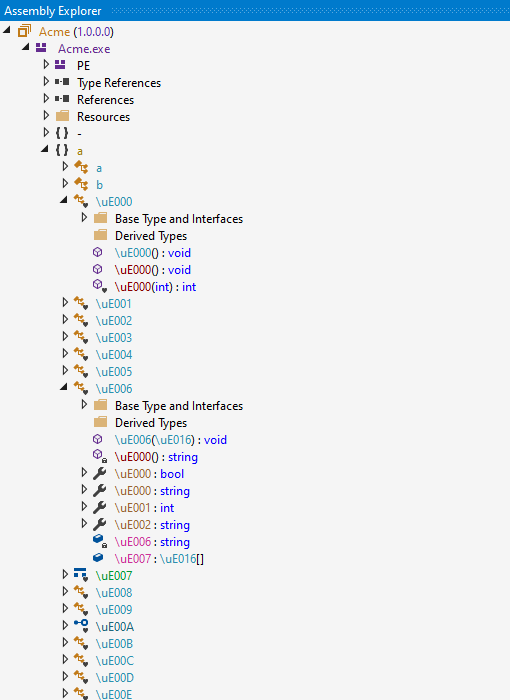
Symbols Renaming
Babel Obfuscator can rename types, methods, properties, events, fields, namespaces and method parameters. The original symbol name are changed, so it is no more possible to recover the meaning of the obfuscated member. This makes code understanding and reverse engineering extremely difficult. You can choose two different renaming convections: alphabet characters and unprintable Unicode symbols. They both minimize the number of character symbol used, reducing the overall metadata size and load time.
Before Renaming
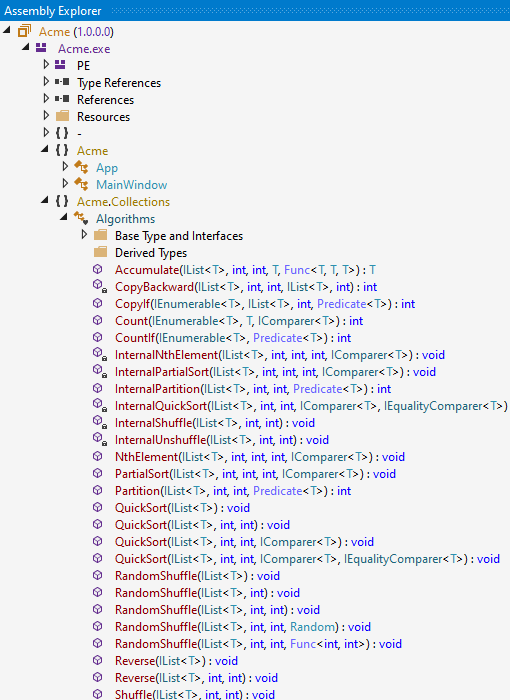
After Renaming
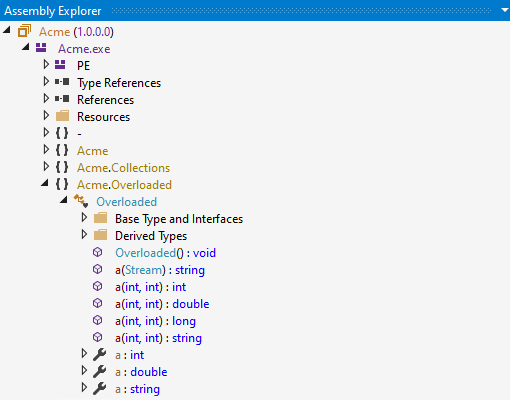
Overloaded Renaming
With overloaded renaming, the same name is used to rename methods with different signatures as long as it is allowed by .NET Framework design rules. This makes it even more difficult for a hacker to reverse engineer the code. Babel also renames overloads when only the method return type differs, making it impossible to entirely decompile the code to high-level languages like C# and VB.NET, in which overloading the return type is not permitted.
Overloaded Disabled
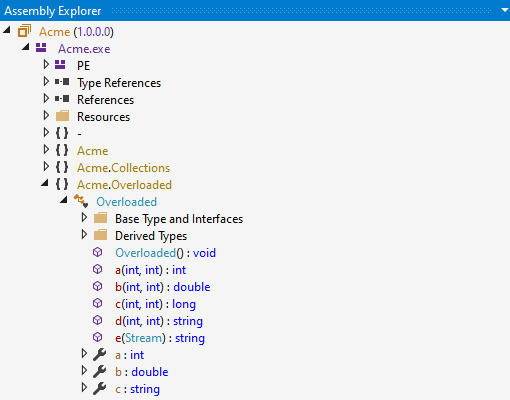
Overloaded Enabled
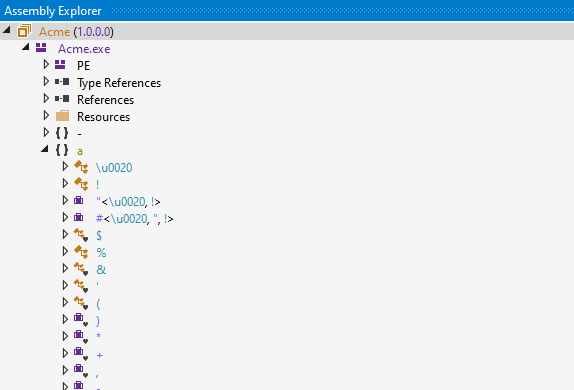
Custom Unicode Characters
Babel accepts custom Unicode character set used to generate obfuscated member names. The user can customize its character set increasing the unreadability of the disassembled code.
Unicode Character Selection
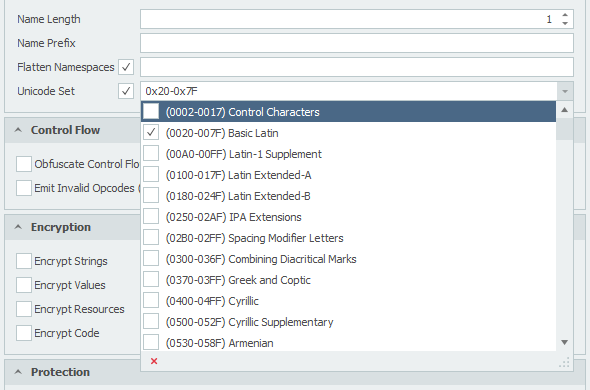
Renaming Result
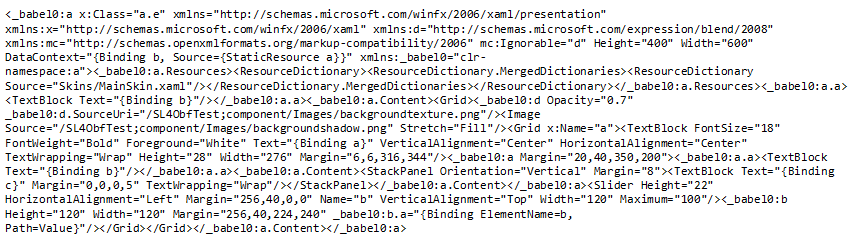
XAML and BAML Renaming
Babel Obfuscator can parse XAML and BAML resources and rename all the members referenced into the XAML/BAML code to produce a better obfuscation increasing the percentage of obfuscated symbols. This also makes your XAML code more difficult to read. Babel is also able to merge into a single assembly file multiple assemblies containing XAML/BAML resources.
XAML Renaming
Code Encryption and Virtualization
Babel Obfuscator brings cutting-edge encryption and virtualization to the forefront of .NET development. This powerful tool encrypts and virtualizes the byte code of methods, rendering them completely indecipherable to any decompiler. It’s designed to work seamlessly with the latest versions of .NET, ensuring code security and compatibility.
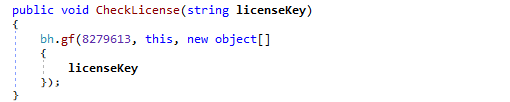
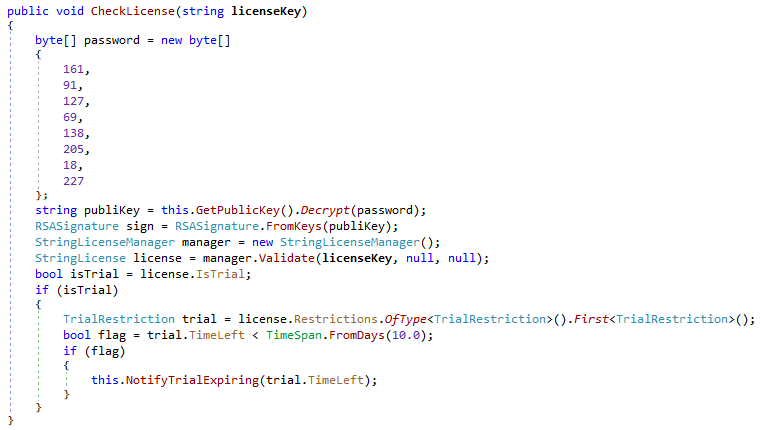
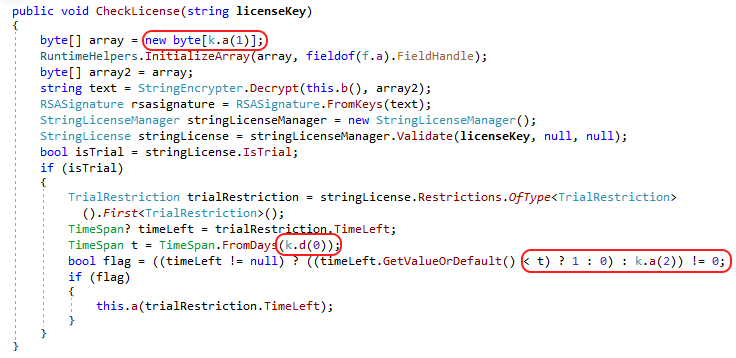
Before Code Encryption
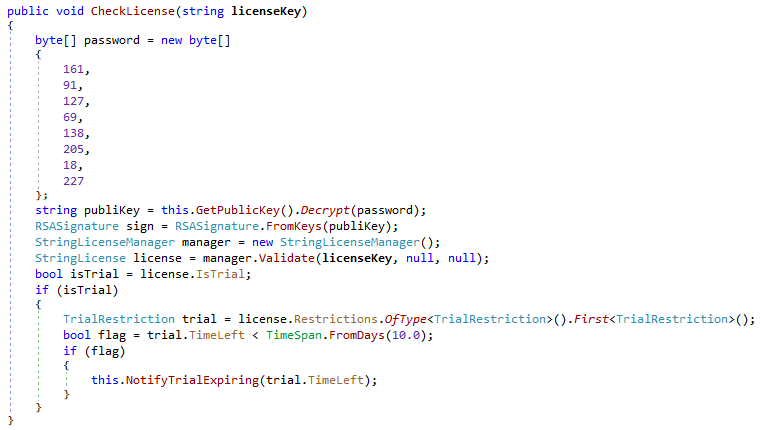
After Code Encryption
Control Flow Obfuscation
Control flow obfuscation consists of changing the execution path of a method. Babel can make if statements more complex to read, insert a number of irrelevant branches, add multiple switch instructions without changing the behavior of the method so that it is very difficult to analyze after the decompilation.
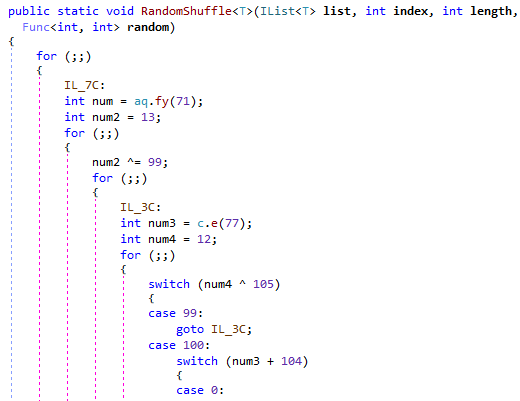
Before Control Flow Obfuscation
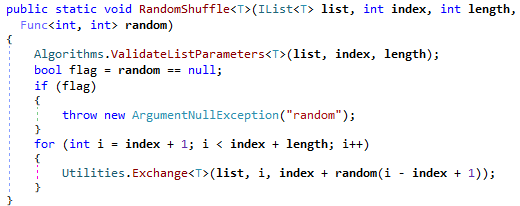
After Control Flow Obfuscation
Inline Value and Array Encryption
Constant values and arrays can contain sensitive information such as encryption keys that the user wants to hide to disassemblers. Babel Obfuscator can to encrypt constant values and arrays, providing an extra protection layer.
Before Value and Array Encryption
After Value and Array Encryption
Resource Encryption
Managed resources can be compressed and encrypted to protect your assets and also to reduce the overall assembly size. The encrypted resources are loaded at runtime when they are eventually needed.
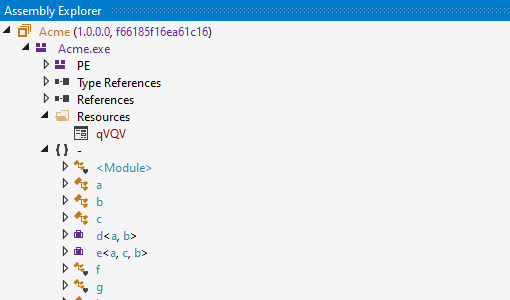
Before Resource Encryption
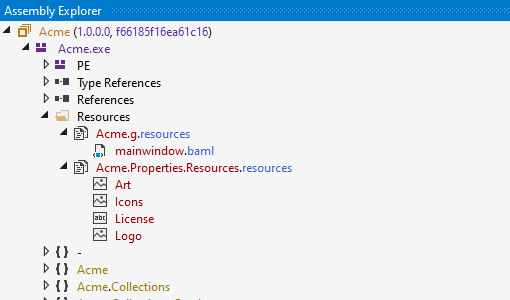
After Resource Encryption
Code Optimizations
Babel Obfuscator can perform a series of optimizations during the obfuscation process. Automatic class sealing and removal of unnecessary attributes can increase the application performance and reduce the overall size on disk. Other optimizations like the removal of System.Enum types, besides reducing the metadata information helps to increase the degree of obfuscation.
Dead Code Removal
Babel can automatically remove unused code and metadata, reducing the assembly size on disk and improving the load time during execution.
Optimizations
Babel can perform a series of optimizations during the obfuscation process. Automatic class sealing and removal of unnecessary attributes can increase the application performance and reduce the overall size on disk.
Automatic class Sealing
Classes that are not used as base classes in an inheritance chain can be sealed. When the JIT compiler sees a call to a virtual method using a sealed type, it can produce more efficient code by calling the method non-virtually.
Cleanup of Unnecessary Attributes
Most of the times, the compiler-generated code it is full of attributes that can be removed without affecting the behavior of the application during execution. Babel can remove any unnecessary attributes applied to a defined type or member reducing the overall disk size of the deployed application.
Const Fields and System.Enum Type Removal
Babel Obfuscator can remove, whenever possible, System.Enum types and const fields defined into the target assembly by replacing their metadata information with the relative constant values. This optimization saves disk space and also makes the disassembled code more difficult to understand due to the use of constants instead of field names.
Disgregate Properties and Events
This optimization performs the removal of properties and events information from the respective metadata tables. Properties and events removal combined with renaming produce a better obfuscation making more difficult to reconstruct the original code.
Inline Expansion
Inline expansion will allow to substitute the call to a method with the instructions in its body inline thereby saving the overhead of function invocation.
Tampering Detection
The .NET Framework can detect an application has been tampered with, when the assembly has been signed. Babel Obfuscator can add an extra layer that will allow you to execute custom logic in case the application has been tampered with.
Deployment
Babel Obfuscator provides a set of tools that make easy to deploy your application and help to debug the obfuscated code.
Merge Assemblies
Babel can merge dependency assemblies into your application assembly, providing an effective solution to single-assembly deployment. Our merge algorithm is NOT based on ILMerge or other third-party tools and is able to merge all kind of assemblies included WPF and Silverlight containing BAML and XAML resources. Babel can also change the visibility of public types when merging referenced assemblies. This change increases the number of symbols that Babel can rename, thus improving the effectiveness of the obfuscation.
Embed Assemblies
Referenced assemblies can be embedded into the main application assembly. Babel can embed multiple assemblies into the main application reducing the overall size of the deployed application.
Handling of Debug Symbols
Babel Obfuscator can handle PDB debug symbol files merging and fixing debug information during the obfuscation process. So it is possible to use debug symbols files with obfuscated assemblies to decode exception stack trace information or even perform step through debugging in Visual Studio.
Decoding of Obfuscated Stack Trace
Babel can decode the obfuscated stack trace in exception reports
